Infrastructure as Code with Terraform
Welcome readers, in this tutorial, we will understand infrastructure as a code with Terraform.
You can also check this tutorial in the following video:
1. Introduction
IaaC or Infrastructure as a code stands is a process of managing and provisioning the cloud infrastructure through the code template with or without manual intervention. IaaC helps to code and document the configuration specifications by avoiding undocumented and ad-hoc configuration changes. The IaaC workflow is a four-step configuration i.e.
- Developers write the code templates
- The pushed code can be version controlled
- Code is reviewed by the team members before merging into the master branch
- Merge the code to the master branch after successful review and trigger the automation/manual process for code provisioning
1.1 Infrastructure as a code (IaaC) benefits
Infrastructure as a Code (IaaC) offers several benefits such as –
- Offers provisioning and configuration consistency across different environments
- Faster deployment
- Reduced cost and human errors
1.2 Managing the cloud infrastructure
To provision and manage the infrastructure via the code templates there are several tools available. Let us take a look at them in detail.
- AWS Cloudformation
- Terraform
- Ansible
- Chef
1.2.1 AWS Cloudformation
AWS Cloudformation is a service that gives developers an easy way to create the aws resources and provision them in an orderly and predictable fashion. A CloudFormation template consists of three main sections:
- The Parameters section is where you define the user-defined values in your template. Using parameters will make your template more reusable. When a user creates a new CloudFormation stack from your template, the CloudFormation UI will provide fields for them to fill out these parameters
- Resources are the meat of your template: that’s where you define which AWS resources should be created when this Template is run through CloudFormation
- Finally, Outputs is where you define the information that should be provided to the user after the resources are created, for example when third-party services need to be configured to operate with your AWS infrastructure
1.2.2 Terraform
Terraform is an open-source tool developed by HashiCorp for building, changing, and versioning the infrastructure safely and efficiently. It is used to manage the infrastructure of the popular cloud service providers and custom in-house solutions. It helps manage both low-level (Compute, Storage, Networking, etc.) and high-level components (such as SaaS, DNS, etc.) Terraform deployment automation is divided into different sections i.e. –
- IaaC – IaaC is popularly known as the Infrastructure as a Code, describing the infrastructure using a high-level configuration syntax. This allows a blueprint of the infrastructure which can be deployed, versioned, and shared for re-use
- Execution Plans – Terraform has a planning step where it generates an execution plan. The execution plan tells the administrator what Terraform will do once applied and helps to avoid any surprises when it creates the infrastructure
- Resource Graph – Terraform builds a graph of all the resources and parallelizes the creation and modification of non-dependent resources. This offers insights into learning the dependencies in their infrastructure
- Change Automation – Terraform allows to apply of complex changesets to the infrastructure with minimal human intervention
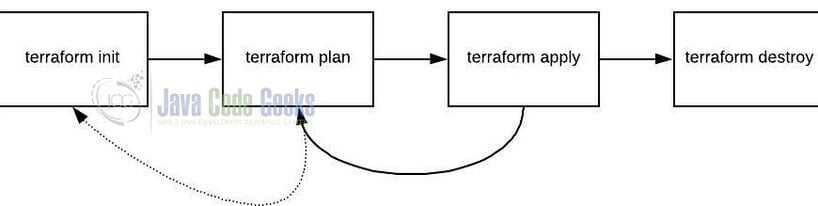
1.2.2.1 Terraform step
To create the infrastructure via the Terraform scripts following commands need to be executed in a sequence. However, details and actions may differ between workflows.
terraform init– Initializing the new or existing terraform configurationterraform plan– Generate the execution plan from the resources specified in the fileterraform apply– Create the infrastructure from the resources specified in the fileterraform destroy– Destroy the created infrastructure
1.2.3 Ansible
Ansible is an open-source agentless automation tool that helps to automate application deployment, cloud provisioning, service orchestration, and other IT tools. Ansible works by connecting nodes and pushing out ansible modules to nodes that are executed and removed after execution. Ansible offers –
- Consistent and lightweight open-source tool to automate and provision the infrastructure
- Agentless capabilities offer security and open ssh security features
- Has a smooth learning curve with modularity regarding plugins, inventories, modules, and playbooks
1.2.4 Chef
Chef is an automation platform that transforms infrastructure into code. Chef tool can run on different platforms such as Windows, Linux, etc, and helps automate how the infrastructure is deployed, configured, and managed across the network.
- Chef has a master agent architecture where the server runs on the master machine and the client runs as an agent on each client machine
- Uses Ruby programming language for automating the infrastructure
- The chef setup costs USD 137 per year
- The chef relies on its server as the authoritative configuration and these servers require cookbooks
1.3 Standardizing deployment workflow
With the growing technological industry standardizing the infrastructure is of utmost importance as the deployment operations are becoming more and more complicated. The time required for the upgrades increases with each complexity. Besides that, the rollback model in the SaaS (Software as a service) adds more complexity to the hierarchy of services. To standard the deployment there are many tools available in the market but the most common tool used among Site Reliability Engineers (SRE) is Kubernetes. Kubernetes is an open-source tool managing containerized applications across multiple hosts. It provides an easy mechanism for deploying, maintaining, and scaling the applications. It offers –
- Standard services like local DNS and load-balancing
- Container restart behavior if it dies
- Pods that wrap around containers thus making configurations easy to build around the collection of containers
- Standard api that applications can call to enable more sophisticated behavior
The other available standardizing tool are –
- Red Hat OpenShift – Redhat product for developing, deploying, and managing containerized applications
- Hashicorp Nomad – Flexible scheduler and workload orchestrator to enable an organization for easy deployment and management of containerized or legacy applications using a single unified workflow
- Docker Swarm – Clustering and scheduling tool for docker containers
- Rancher – Open-source multi-cluster orchestration platform to deploy, manage, and secure enterprise Kubernetes
- Mesos – Open-source cluster manager with support for container storage interfaces
1.4 Track your infrastructure
Tracking the infrastructure talks about monitoring the created IT or application infrastructure. Infrastructure monitoring refers to the diagnosis of the performance and availability issues across the deployed technology stack. The monitoring helps to take proactive actions before the identified problems become severe or critical. The monitoring framework follows the below principles i.e. –
- Prioritzation of jobs into critical to minor
- Creating the alert resolution processes for automated triggers or alerts
- Combine the different monitoring tools such as both on-premise and cloud
- Review the infrastructure and application metrics daily
- Conducts performance and load test on applications
1.5 Collaborate
Collaboration in IaaC is an important aspect as it helps developers and the operations team to automatically manage and provision the infrastructure through code instead of making configuration changes through a manual process.
2. Summary
In this tutorial, we saw the explanation of infrastructure as a code (IaaC) and terraform in little detail. That is all for this tutorial and I hope the article served you with whatever you were looking for. Happy Learning and do not forget to share! Happy learning and do not forget to share.